By Oiwan Lam
China is one of the countries that has been hit hardest by the ransomware program known as “WannaCry” launched on 12 May, which infected over 230,000 computers in 99 countries in just one day.
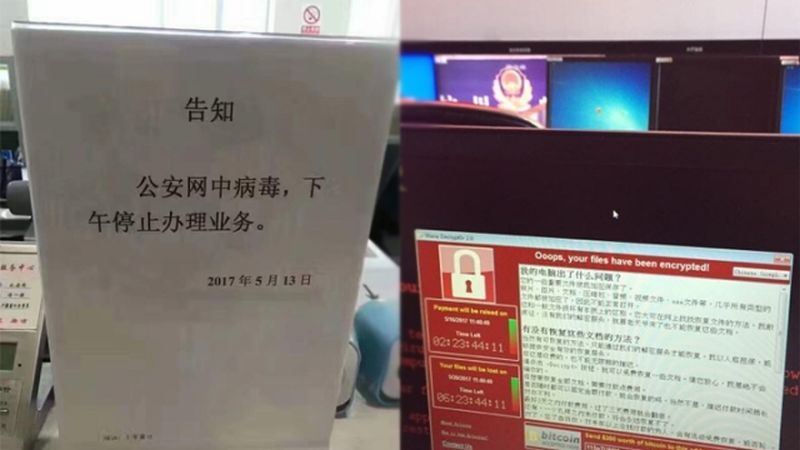
China’s National Computer Network Emergency Response Center has confirmed that by 14 May, half of the infected IPs were located in China. The attacks have affected about 30,000 institutions, including universities, immigration checkpoints and oil stations.

The ransomware, which is believed to exploit the “Eternal Blue” loophole developed by the US National Security Agency (NSA), attacks computers running Microsoft Windows operating systems and locks users out of their own computers by encrypting their files. It demands that they pay USD US$300 in Bitcoin in exchange for de-encryption. Once connected to the Internet through port 445 (a port for document sharing protocols), all computers running a Windows operating system would be subjected to attack if they had not downloaded the security update patches issued in March 2017.
The ransomware was briefly contained with the discovery of a “kill switch” by a British researcher, but on May 14 a new version was released.
Chinese computer users may be more vulnerable to the attack as many commonly use unlicensed (i.e. pirated) or outdated versions of Windows OS and thus do not receive security updates.
To make matters worse, many computer users were unaware of the coming of the attack as very few local media outlets reported about the security threats.
Though a majority of Internet service providers in China have blocked port 445, which is mainly used for Windows operating system file-sharing, to avoid potential massive attack targeting Microsoft Windows, many public service institutions, including universities, public security offices and oil stations have not blocked the port.
University campuses have been among the worst affected. Universities all over the country, including Qinghua, Beida, Shanghai Jiaotong and Shandong university have been infected. A large number of student theses and research projects have been (and remain) encrypted by the ransomware. Domestic media outlets reported that:
[mks_tabs nav=”horizontal”]
[mks_tab_item title=”English”]
By 20:00 on 13 of May, hundreds of thousands computers from 29,372 institutions have been attacked by the ransomware. 4341 education related institutions have infected cases…
[/mks_tab_item]
[mks_tab_item title=”Original”]
截至到5月13日20点,国内有29372家机构组织的数十万台机器感染,其中有教育科研机构4341家中招…
[/mks_tab_item]
[/mks_tabs]
State media outlet Xinhua report quoted the National Computer Network Emergency Response Center saying that:
[mks_tabs nav=”horizontal”]
[mks_tab_item title=”English”]
By 10:30 on 14 of May, the National Computer Network Emergency Response Center had detected 2,423,000 IPs under the attack as a result of Eternal Blue Exploit; the number of IPs inflected by the ransomware is more than 35,000 [worldwide] and within China, about 18,000 IPs have been infected.
[/mks_tab_item]
[mks_tab_item title=”Original”]
截至14日10时30分,国家互联网应急中心已监测到约242.3万个IP地址遭受“永恒之蓝”漏洞攻击;被该勒索软件感染的IP地址数量近3.5万个,其中中国境内IP约1.8万个。
[/mks_tab_item]
[/mks_tabs]
In addition to the education sector, a number of immigration checkpoints were paralyzed because the public security network was infected.
On social media, public security officials in Xiangshui City, Jiangsu Province reported that its immigration system was under attack and they had to close the immigration checkpoint service. Netizens reported that Shanghai city and Beijing’s Chaoyang immigration offices were also paralyzed because of the ransomware attack.
At midnight on 13 May, a large number of PetroChina’s auto oil-fill machines were paralyzed and the system not restored until 12pm on 14 of May.
In the face of the new version of the ransomware “WannaCry2.0”, which cannot be stopped by the so-called “kill switch”, Chinese authorities have issued a warning via major web portals, media outlets and university networks in an effort to contain the spread of the ransomware.
Thus far, there has been little evaluation of why China has been one of the most vulnerable countries in this ransomware attack. Official media outlets suggested that the spread of the ransomware was caused by university students using the school network to play online games. But this does not explain why public security and oil service networks have also been infected.
This article first appeared on Global Voices.
